Social Media Hacking
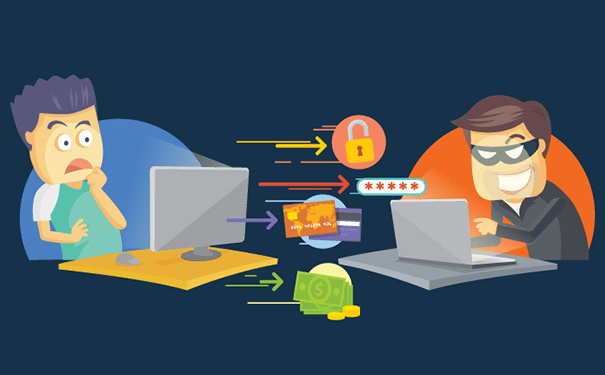
How to Hack Social Media Account - Hacking social networks has now become a regular occurrence over the Internet all over the world. Instagram, Twitter, YouTube, Email, Facebook, and several other online accounts are being hacked almost every day. Your accounts are not safe from Social Media hackers even if you have strong passwords and extra security measures. This article will take you through a few common tactics used to hack social media accounts.
Common Tactics Used to Hack Social Media Accounts
-
Dictionary
This hacking attack automatically tries every word in a defined “dictionary” against the password. This dictionary is a small file containing the most commonly used password combinations. For instance, qwerty, password, princess, 123456, and baseball to mention a few. -
Rainbow Table
This is usually an offline password attack. For instance, an attacker has attained a list of usernames and passwords, but they are encrypted. The encrypted password is then hashed. This means it looks different from the original password.
-
Keylogger
This surveillance software can be installed on a system and it has the potential to record every single keystroke made on that system. -
Brute Force
In a brute force attack, an attacker tries every possible character combination. Attempted passwords will match the specifications for the complexity rules, for example, including one lower-case, one upper-case, your pizza order, decimals of Pi, and so on. A brute force attack also tries the most commonly used alphanumeric character combinations first such as 1q2w3e4r5t, qwertyuiop, and zxcvbnm. -
Phishing
This is not exactly a hack, however, falling prey to a phishing attempt generally ends badly. Generally, a phishing email works in the following manner:Target user receives a spoofed email claiming to be from a well-known organization or business concern
- A spoofed email will need instant attention, featuring a link to a website
- Link to the website links to a false login portal, mocked up to appear just the same as the legitimate site
- Innocent target user enters their login credentials, and is either told to try again or get redirected
- User credentials are sold, stolen, or used for illegal purposes.
-
Malware
Falling prey to malware is yet another sure way to lose your login credentials. Malware is out there just to do massive damage. If the malware variant features a keylogger, all of your accounts could get compromised. Alternatively, the malware could precisely target private data, or introduce a remote access Trojan to steal your credentials.
Having discussed some of the commonly used hacking techniques, it has thus become a necessity for you to install security software capable of protecting your website and providing you with a wide range of security-related features. This software should not only avoid damages but should also lessen the stress of website security. To secure all your online activities and your PCs, you can use Comodo cWatch.
Social Media Hacking Prevention Tool
cWatch is a Managed Security Service developed by Comodo. This web security solution is perfect for websites and applications and is available with a Web Application Firewall (WAF) provisioned over a Secure Content Delivery Network (CDN). It is a fully managed solution from a 24/7 staffed Cyber Security Operation Center (CSOC) of certified security analysts and is powered by a Security Information and Event Management (SIEM) center capable of leveraging data from more than 85 million endpoints to detect and mitigate threats even before they occur. Malware Removal and PCI Scanning are the other key features offered by Comodo cWatch.





