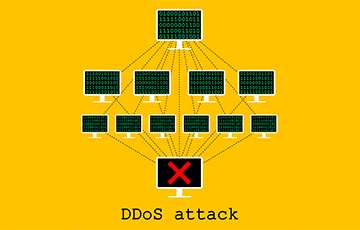
How to Prevent DDoS Attacks?
For organizations having an online presence, protecting web applications and server infrastructures from distributed denial-of-service (DDoS) attacks is no longer a choice. The advent of DDoS-for-hire services has greatly lowered the bar for those capable of carrying out an assault, making all web entities a potential target.
Successful DDoS attacks negatively impact an organization's reputation besides damaging existing client relationships. When a DDoS attack hits your network, it would take a long time for the security/network staff to fully realize it is, in fact, a DDoS attack that is affecting the services, and not just a failing server or application. A lot more time may pass before the actual mitigation of the threat begins to take effect.
Why do DDoS attacks happen?
The reasons why a DDoS attack takes place can be divided into three main categories:
- Extortion - The attacker threatens an attack and demands money to avoid it.
- Retaliation - The attacker responds to something you did or said, or just doesn't like you.
- Misdirection - The attack is intended to distract you from some other attacks happening elsewhere.
How to Stop and Prevent DDoS Attacks?
Key measures for stopping and preventing a DDoS attack are discussed below:
1. Understand that any type of business is vulnerable
Money is mostly involved in many DDoS attacks. According to cybersecurity analysts, blackmail and ransom are the most common motives behind DDoS attacks. In such attacks, hackers interrupt web services and hold it against a ransom. After the ransom amount is paid, the attack stops and services again become available to customers.
2. Install a WAF
A Web Application Firewall (WAF) is always considered to be the best defense against the most common types of DDoS attacks. Once identified, rules and policies are applied to block such attacks based on malicious IPs, bot signatures, and so on. WAF will help you stop a DDoS attack effectively.
3. Monitor application traffic continuously
An application layer distributed denial of service attack is introduced by hiring bots, machines, or by taking control of remote systems. These components are used for producing false requests to a targeted server. With such a huge number of fake requests, cybercriminals attempt to make the services of an application or server unavailable for days, hours, or weeks. A successful DDoS attack can consume huge chunks of the processing speed, bandwidth, and memory in order to slow down and/or interrupt applications.
Only with continuous monitoring, you will be able to protect your business by efficiently detecting and preventing DDoS attacks. Such monitoring will succeed in delivering actionable data on attack vectors to define prevention policies.
4. Inhouse DDoS Security or Managed App Security
Setting up a dedicated team will allow you to monitor attacks and take actions efficiently and swiftly. A team like this will not only offer 24×7 traffic monitoring and DDoS attack mitigation, but will also provide complete application security including:
- Periodic penetration testing.
- Custom WAF rules to block attacks.
- Business logic tests on all applications to detect zero-day threats, vulnerabilities, and automated application risks.
- Latest security notifications to protect your applications from known vulnerabilities.
- Round-the-clock monitoring to collect information such as User ID if authenticated, IP address, navigation/user behavior, GEOlocation, and machine fingerprint that can help gain intel about the attacker's methodologies to use that data in developing more aggressive blocking rules from these attackers
5. Install a Protection Tool
This is a very crucial step you will have to follow in order to stop DDoS attacks. You will have to install a tool capable of detecting and preventing such attacks allowing your business to remain safe and also protecting all sensitive and essential data of different website users. All these features and many more can be obtained from a web security tool called cWatch, developed by Comodo.
Comodo cWatch Web is a Managed Security Service perfect for websites and applications. It is available with a Web Application Firewall (WAF) that can prevent DDoS attacks. This web security solution has a Secure Content Delivery Network (CDN) and is fully managed by a 24x7x365 staffed Cyber Security Operation Center (CSOC) of certified security analyst. cWatch is powered by a Security Information and Event Management (SIEM) capable of leveraging data from more than 85 million endpoints in order to detect and mitigate threats even before they occur.
As an effective and reliable tool capable of stopping DDoS attacks, cWatch also provides malware detection scanning, preventive methods and removal services to enable businesses to take a proactive approach to safeguard their business and brand reputation from attacks and infections. Vulnerability scanning is also available, and this provides online merchants, businesses, and other service providers handling credit cards online with an automated and simple way to stay compliant with the Payment Card Industry Data Security Standard (PCI DSS).





