What is a Web Application Firewall (WAF)
A Web Application Firewall (WAF) is a specialized form of online defense designed to protect web applications by filtering and monitoring HTTP traffic between a web application and the Internet. It is a shield between web applications and the Internet, acting as a protective barrier against many forms of web-based security threats.
Understanding the Functionality of WAF
Unlike traditional firewalls that guard the perimeter of a network, WAFs focus specifically on web applications. They are adept at understanding and scrutinizing web-based traffic to detect and deter attacks at the application layer. This involves analyzing GET and POST requests used to send and receive data from web applications.
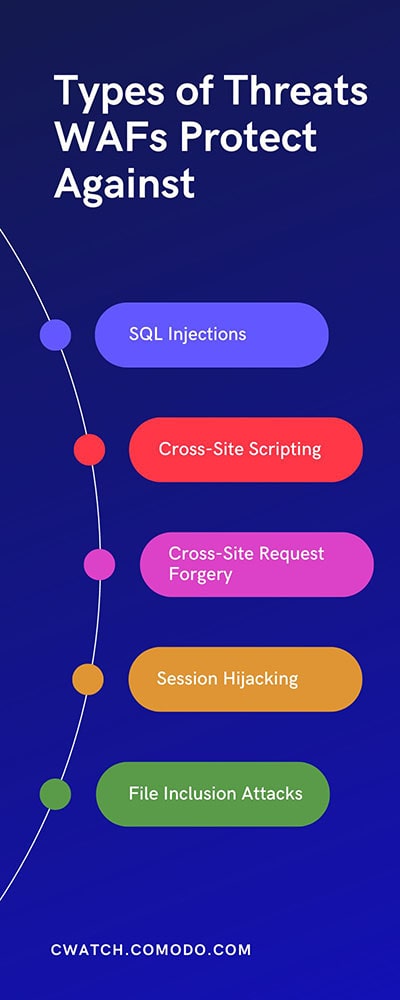
Types of Threats WAFs Protect Against
WAFs are primarily designed to defend against attacks stemming from the OWASP (Open Web Application Security Project) Top 10 list of threats, which include:
- SQL Injection Attacks occur when attackers use malicious SQL code to manipulate a database behind a web application.
- Cross-Site Scripting (XSS): This involves injecting harmful scripts into web pages viewed by other users, often stealing data or defacing websites.
- Cross-Site Request Forgery (CSRF): CSRF tricks a user into submitting a malicious request, potentially altering data or performing unauthorized actions.
- Session Hijacking: Attackers might hijack a user session to gain unauthorized access to sensitive information.
- File Inclusion Attacks: These happen when attackers trick a web application into running or exposing files on a web server.
How WAFs Operate
WAFs operate through a set of rules or policies, often referred to as rulesets. These rulesets determine what traffic is considered safe and what should be blocked or challenged. There are three primary models through which WAFs operate:
- Whitelist Model: Only allows traffic that meets specific criteria. This model is highly secure but can be restrictive.
- Blocklist Model: Blocks known malicious traffic based on signature patterns. It's effective against known threats but might not catch newer, sophisticated attacks.
- Hybrid Model: Combines aspects of both allowlist and blocklist models for a balanced approach.
Customization and Configuration
A key feature of WAFs is their ability to be customized according to the specific needs of a web application. Administrators can configure rules and policies to align with their application's security requirements, ensuring robust protection and optimal performance.
Compliance and Regulatory Requirements
WAFs also play a crucial role in helping organizations meet various compliance and regulatory requirements, such as the Payment Card Industry Data Security Standard (PCI DSS). By securing web applications, WAFs ensure that sensitive data, such as credit card information, is safeguarded against breaches.
Cloud-Based and On-Premises WAFs
WAFs can be deployed in various environments, including on-premises and cloud-based services. Cloud-based WAFs offer the advantage of scalability and ease of management, while on-premises WAFs can offer greater control over the security environment.
Why Choose cWatch?
In Web Application Firewalls (WAFs), cWatch is a premier choice for businesses seeking robust, efficient, and comprehensive web security solutions. Here’s why cWatch is a preferred choice for protecting web applications:
Advanced Threat Protection
cWatch leverages cutting-edge technology to offer superior protection against the most sophisticated web threats, including those listed in the OWASP Top 10. Its dynamic threat intelligence continuously evolves, safeguarding your web applications against the latest vulnerabilities and attack vectors.
User-Friendly Interface
One of the standout features of cWatch is its intuitive, user-friendly interface. This ensures that even users with limited technical expertise can easily navigate and manage their web security settings. It simplifies the complex task of web application security, making it accessible to all levels of users.
Customizable Security Rules
cWatch provides a high degree of customization in its security rules, allowing businesses to tailor their security posture according to their specific needs. This flexibility ensures that cWatch can adapt to the unique security requirements of various web applications, from tiny blogs to large e-commerce sites.
Real-Time Monitoring and Reporting
With real-time monitoring and detailed reporting capabilities, cWatch offers businesses a clear view of their web security status. This feature enables quick identification and response to potential threats, ensuring minimal impact on the web application’s performance and user experience.
24/7 Support and Expert Assistance
cWatch prides itself on offering round-the-clock support from cybersecurity experts. This ensures that businesses have access to professional guidance whenever needed, providing peace of mind and promptly addressing any security concerns.
Compliance and Data Protection
For businesses concerned with regulatory compliance, cWatch is an invaluable tool. It helps comply with standards like PCI DSS, HIPAA, and GDPR by providing robust security measures to protect sensitive data from breaches and unauthorized access.Cloud-Based Solution
As a cloud-based WAF, cWatch offers the advantages of scalability and ease of deployment. Businesses can benefit from high-level security without significant infrastructure investment, making it a cost-effective solution for companies of all sizes.
Integrated Approach to Security
cWatch is not just a standalone WAF; it's part of a comprehensive suite of security solutions. This integrated approach ensures that all aspects of web security are covered, from malware detection to vulnerability scanning, providing a holistic defense strategy.
Web Application Firewall (WAF) FAQ
Answer: A WAF is a security solution designed to protect web applications by filtering and monitoring HTTP traffic between a web application and the Internet. It applies rules to an HTTP conversation to cover common attacks such as SQL injection and cross-site scripting (XSS).
Answer: Any organization that operates web applications, especially those handling sensitive data, needs a WAF. This includes e-commerce sites, online service providers, and businesses with an online presence, which are frequent targets for cyber attacks.
Answer: While WAFs provide robust protection against many types of web-based attacks, especially those targeting application-layer vulnerabilities, they are not a standalone solution for all cyber threats. Using them in conjunction with other security measures for comprehensive protection is recommended.
Answer: No, a WAF is designed to protect web applications and operates at the application layer. At the same time, a regular firewall typically provides network-level protection, driving at lower levels of the OSI model to monitor and control incoming and outgoing network traffic.
Answer: An Intrusion Detection System (IDS) and an Intrusion Prevention System (IPS) are focused on identifying and preventing malicious network activities. In contrast, a WAF is specifically tailored for web applications, protecting against threats that exploit application-layer vulnerabilities.
Answer: Essential features in a WAF include real-time traffic monitoring, customizable rule sets, protection against OWASP Top 10 threats, integration capabilities with existing security tools, ease of deployment and management, and reliable support and maintenance services.






